
Phishing Email
Here is a new spin on an old trick. This phishing attacker hopes that you will fall for the warning and click on the link to change your password. “Phishing is the fraudulent practice of sending emails purporting to be from reputable companies in order to induce individuals to reveal personal information, such as passwords and credit card numbers” (Ofxord Dictionary). When you click on the link in the email you are taken to a web page (hosted on yolasite.com). On this web page you would enter in your username and password.
When you “change” your password, you are actually “changing it” on a fake website specifically setup to capture email usernames and passwords. Then the hijacker will exploit those email addresses. In this case the email subject is trying to convince you that it expires today, we have also see it “Password Will Expire Within 12hrs!!” and “Password Will Expire Within 10hrs!!” and “Password Will Expire Within 8hrs!!“.
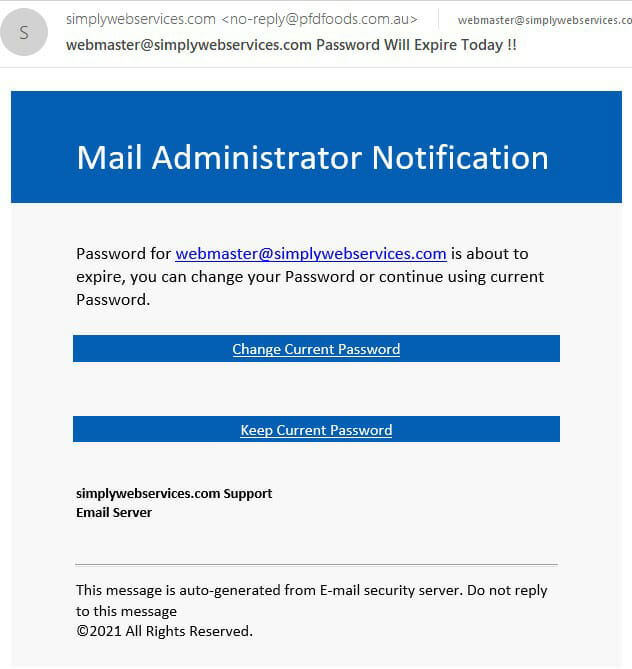
The email samples we have are coming from ideoti.com, which is using cloudflare.com to help mask the real destination. The link in the email is redirected several time, ultimately going to yolasite.com which is a legitimate web hosting company.
When you click on the link in the email, you get (redirected)
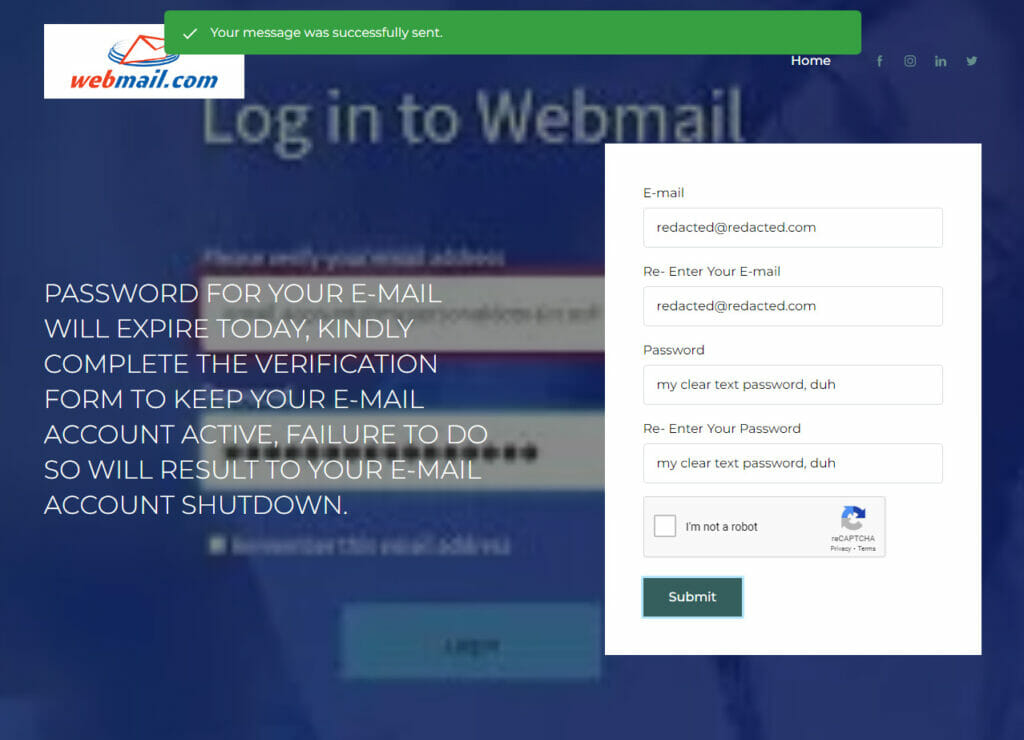
The ultimate destination of the input username and password are sent via ws-platform.net (a legitimate website for forms that you can use on your website). The destination is encrypted and encoded as “fJ_Jlkr-tp7o64RZk69HmhyMDzseEVLTRUi-jPjW1qk=:h8F_JRcSpgbtE18Ca5w_DLeNu7-734l3yKh_gvCM7ug=“. I find it interesting that the phisher went to the trouble of using reCAPTCHA, but they didn’t bother to add the “hidden” attribute to the form to hide the password.
Why Me?
The emails are not targeted toward you, your email address was likely on a list of addresses that the phisher purchased. You were not a target specifically.
What To Do If You Fell for this Scam?
If you went to a web page like this and entered in a valid email address and password, you need to go to the actual place where your email is hosted and change your password there. I also recommend that you let your hosting company know, so they can be on the look out for this particular phishing attack.